Calls for improvements in detecting suspicious banking transactions
The issue has come under renewed focus following a Sessions Court ruling ordering a bank to compensate a customer RM166,000 over suspicious online transactions that went undetected.
As scams evolve, banks are facing heightened urgency to identify unusual transaction patterns and act fast, particularly as fraudsters exploit human behaviour and then move in to breach banking systems.
At a Bank Negara workshop on consumer protection and fair conduct reforms, its officers said existing laws protect the confidentiality of customer information and personal data in the financial sector.
“Financial institutions are robust but there is always room for improvements,” the officers said yesterday.
They said enforcement actions had been taken in instances where breaches were identified, including requiring the institutions involved to implement corrective action plans.
The officers also said Bank Negara continued to monitor banks on consumer protection and compliance matters.
In its latest annual report, the central bank stressed the need to strengthen fraud detection systems and reinforce internal safeguards to combat sophisticated online scams.
The central bank said banks and non-bank financial institutions were required to adopt advanced fraud detection measures and strengthen internal safeguards to quickly intercept suspicious transactions.
It also stressed for a proactive approach to prevent fraudulent transactions from escalating.
The central bank said that in recent years, financial institutions had strengthened various security measures including tighter fraud detection rules and triggers, cooling-off periods for new device registrations and stronger authentication methods.
These measures contributed to a 52% decline in unauthorised fraudulent transactions involving malware and phishing reported in 2024, and prevented over Rm399mil in attempted fraudulent transactions, it said.
However, Bank Negara also acknowledged that fraud patterns were becoming increasingly complex and harder to distinguish from genuine customer activity.
Bank Negara said banks and consumers shared responsibility for safeguarding digital banking security, but reiterated that financial institutions had to determine whether weaknesses in their internal controls contributed to fraud incidents.
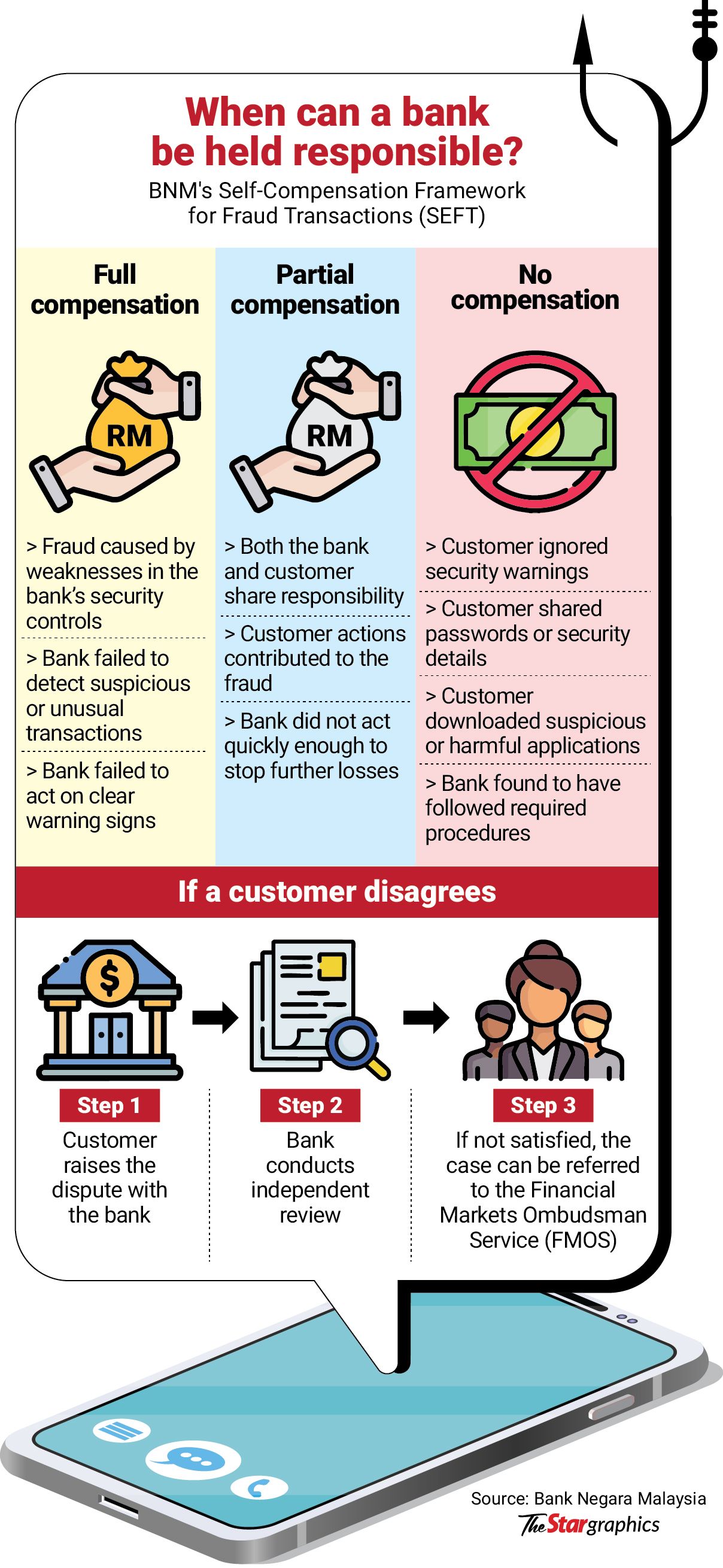
It also introduced the Selfcompensation Framework for Fraud Transactions (SEFT) under its Policy Document on Ensuring Fair Treatment for Victims of Unauthorised e-banking Transactions.
SEFT outlines how banks should assess fraud cases and determine compensation based on the responsibilities of both financial institutions and customers.
According to Bank Negara, more than 95% of online fraud cases in Malaysia involved authorised transactions – where victims were manipulated into willingly transferring money to scammers.
Federation of Malaysian Consumers Associations (Fomca) vice-president Datuk Indrani Thuraisingham agreed that banks should adopt more proactive intervention measures when transactions appear inconsistent with a customer’s normal behaviour.
“Banks are clearly not doing enough. Fraudsters now exploit human behaviour more than banking systems,” she said.
“Banks must transition from passive logging to active, pre-emptive intervention.”